Thoughts on Data Security
The recent Equifax data breach got me thinking more in depth about the role RustProof Labs plays in cybersecurity. I'm not just talking about how we approach cybersecurity to protect ourselves and our clients, but instead the larger discussion about the need for more companies and individuals to take cybersecurity seriously.
Brian Krebs recently wrote about an egregious error made by Equifax that apparently isn't even related to the main breach:
It took almost no time for them to discover that an online portal designed to let Equifax employees in Argentina manage credit report disputes from consumers in that country was wide open, protected by perhaps the most easy-to-guess password combination ever: “admin/admin.”
This kind of vulnerability is inexcusable considering the magnitude of the data that Equifax is responsible for securing.
Our Personal Data is Priceless
To me, my own personal information is worth more than a bank vault full of gold. I want everyone who stores data about me to treat it that way. Unfortunately that is not the reality today.
We obviously expect that our data is treated with special attention and security, yet we realize and, sadly, accept that our data is treated like any cheap commodity. Though one major difference between our personal data and a cheap commodity is that our data is sold at premiums prices!
Security is Your Responsibility
- If you are a professional and work with data, the security of that data is your responsibility.
- If you are an organization that has data, the security of that data is your responsibility.
- If you happen to be an organization who's life-blood is data, such as RustProof Labs (ahem, Equifax), this is even more paramount.
Yes, it's a responsibility. You can't just blame a data breach on "the bad guys" if you're lazy with your security. It is your fault my SSN is out there, from your data set that you allowed to be breached.
Disclaimer: At the time of writing I don't know all the details about the "how" of this Equifax breach, but so far the evidence points to an complete absence of proper security.
Security at RustProof Labs
As I was trying to decide how to talk about how we approach cybersecurity at RustProof Labs, I decided the best way to start was to highlight some of my previous writing here on the RustProof Labs blog. In January 2014 I wrote "Ensuring data integrity and security is the most important thing to me..." Later in 2014, the #1 reason I used to justify a bunch of work was security. This opinion still holds true, too.
To those folks I would ask why they would trust a mission critical app to outdated technology, but hey that's just me...
I've complained about how many sources of "information" recommended using outdated technology and taught terribly insecure methods. Part of our security problem is that new programmers and developers are not taught enough about proper security controls. Another part of the problem is that "security is hard" and some programmers do take the easy way out.
I also wondered why SQL Injection is the #1 Vulnerability In September 2017, injection is still the biggest problem on OWASP's list, and I still don't know why. Sanitize input + parameterize queries = No SQLi. As with many cybersecurity vulnerabilities, the solution isn't tough. You just have to do it.
Our Code of Ethics
In 2016 RustProof Labs adopted our current Code of Ethics. There's one point in there that I want to highlight:
I am obligated to report all system vulnerabilities that might result in significant damage.
This obligates everyone bound by our Code of Ethics to report vulnerabilities, helping to create a culture of reporting problems as they are discovered. In our case, problems are logged in Jira with a "Security" tag. These issues are given the highest priority and are researched and dealt with appropriately.
Security Scans
Do you ever check if your doors and are closed and locked? How about if you ever click your car's key fob one extra time, just in case it was accidentally unlocked? It makes you feel good, right?
The problem with cybersecurity is that it is taken as a fire-and-forget deal. It isn't. Cybersecurity requires continuous maintenance and verification. One regular task I have is to run various security scans, so I'm out there proactively looking for problems. What had been secure last month or last year may no longer be secure. Configurations probably have been changed.
We regularly scan our systems for new security vulnerabilities, and when issues come up like Shellshock, Heartbleed, and DROWN we check and patch our systems ASAP. Our security scans and support doesn't stop with RustProof Labs infrastructure, we offer this assistance to our clients as well. Recently, one of our routine scans detected a server misconfiguration on a client's public facing server. We contacted them to let them know what we had found, and they had it fixed on their end right away.
Easy Check
If you are responsible for a public facing website, do yourself a favor and run this security check. It's free, runs in about two minutes, and will tell you exactly what is wrong that needs fixing to make your website more secure.
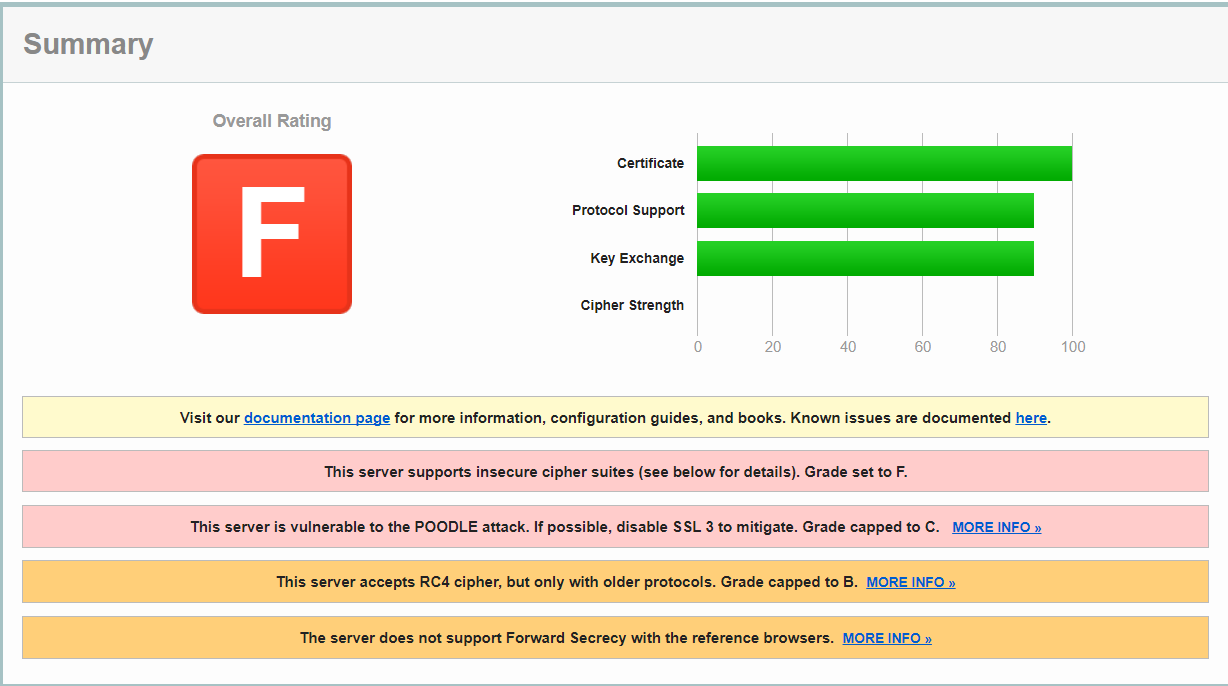
Don't be This
There is no reason to support SSL v3, vulnerable to the POODLE attack, among other very major issues. The POODLE attack came up 3 years ago, not patching this by now is not acceptable.
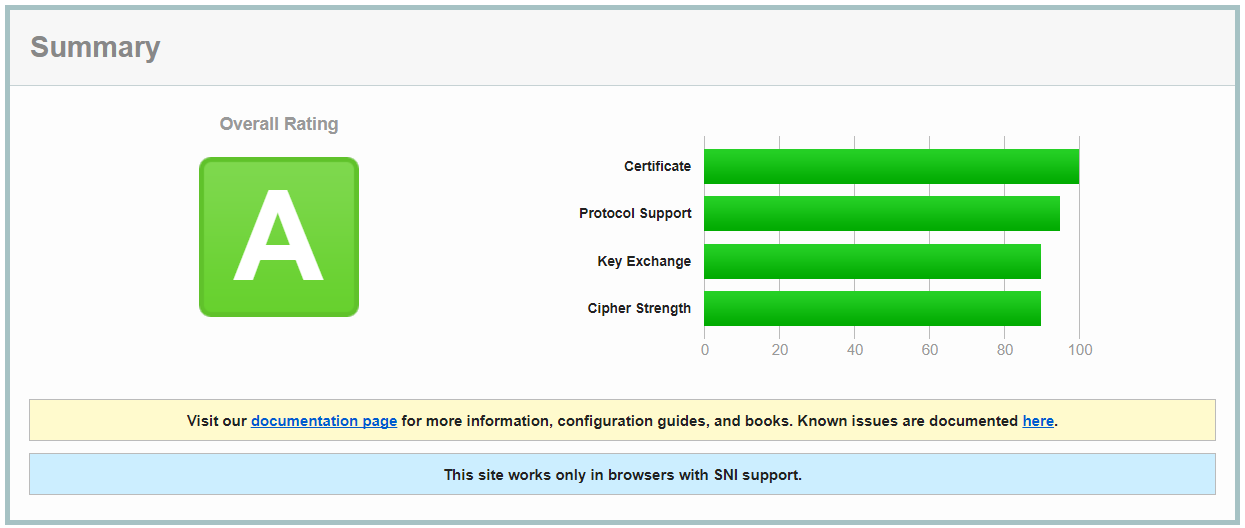
Role Model
Getting an "A" isn't that difficult. It doesn't fix everything but it doesn't leave open doors. This screenshot is for a local non-profit's website with a very limited budget.
Security all the Time
Your cyberseurity must be considered with all the data you store, and in every technical project from day 1. Your systems also need to be tested and re-evaluated periodically. Annual is probably the least frequently I would recommend between evaluations. Cybersecurity is not a fire-and-forget operation, it does represent an expense to the business, but there's no excuse to shirk such a responsibility.
Summary
Every business has data in some form and I would assume that the majority have at least some sort of presence online. At least in the form of email and a basic website. I implore every data professional and organization to treat the security of these systems with the respect it deserves.
Even with improved security, the bad guys will still probably find a way in, but they'll have to work a lot harder. If you can't prove you took cybersecurity seriously, you can't just blame the bad guys.
